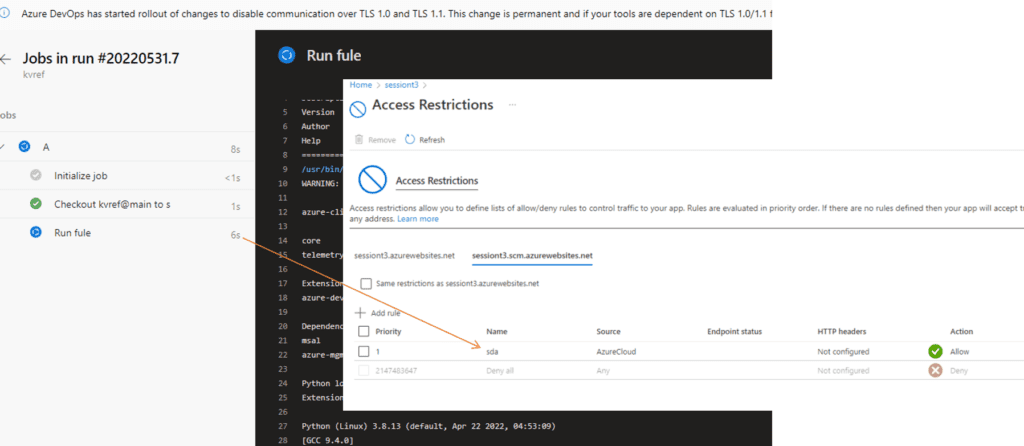
Most typical reason I see that the SCM endpoint is not secured on App Services is that these apps are often updated by MS hosted Azure DevOps agent.
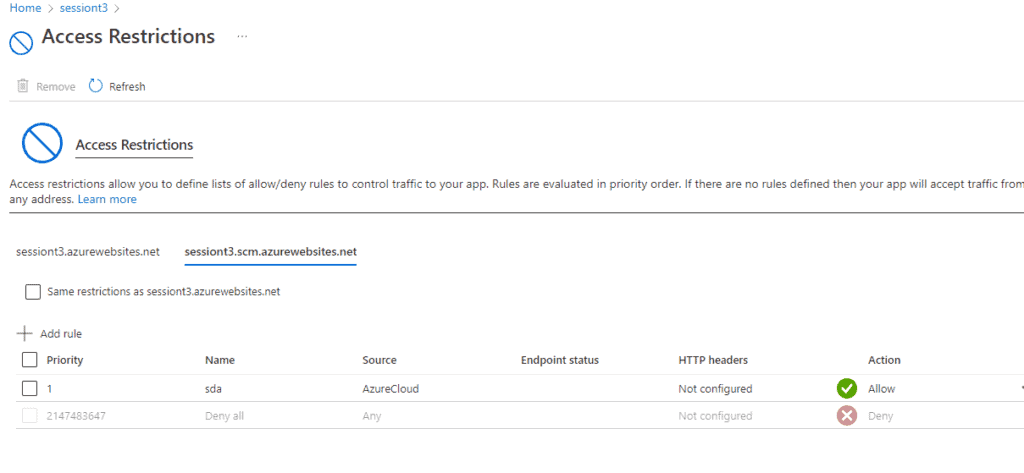
Luckily you can increase the security of your app service greatly – If you previously did not have any network restrictions on SCM endpoint, you can now have the SCM endpoint restricted to ’Azure Cloud’ – Yes that is still lot of attack surface, but is exponentially less than the whole internet being able to probe your App Service.
Setup
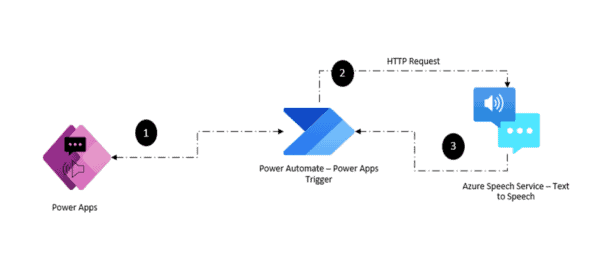
Example pipeline below using Service Connection with Client Credentials (certificate)
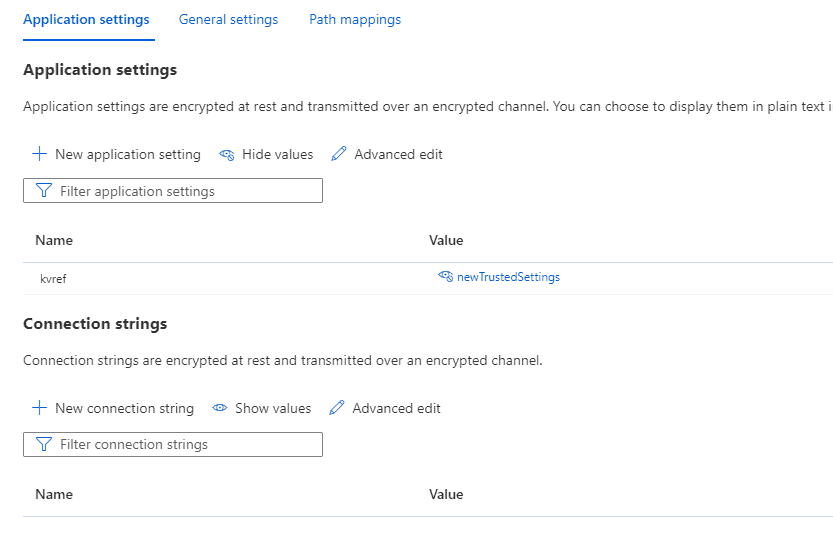
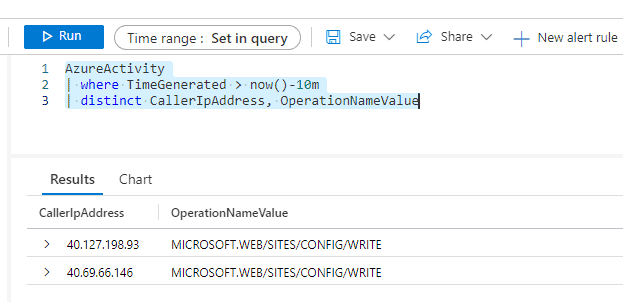
- Pipeline updates app setting for network restricted web app
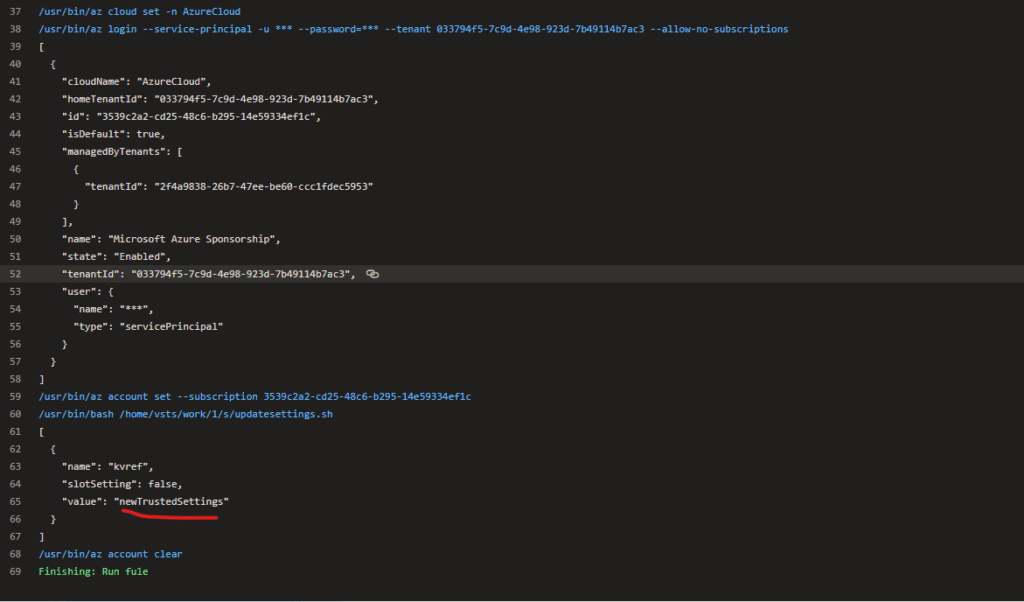
- Setting is updated as follows to app service
- Network restrictions uses the ’tag’ setting for ’Azure Cloud’
This blog featured as part of Azure Week. Find more great Azure content here.
About the Author:
Security Consultant, Hacker, NodeJS dev/fanboy and blogger!
I am security consultant doing security related work, and security tooling development side projects with approx. +10 years into IT industry
My work and interests consists heavily around Identity And Access management, and securing Azure Services, and developing new services with NodeJS.
In terms of recognition I am really honored and humbled to be selected as one of the Microsoft MVP’s globally for Azure Award category. I’ve been also publicly recognized by MSRC in 2019 for my security research efforts related to MSRC Bug Bounties
Reference:
Santasalo, J. (2022). Azure Devops – Update network restricted App Service via Microsoft-hosted Azure DevOps agent. Available at: https://securecloud.blog/2022/05/31/azure-devops-update-network-restricted-app-service-via-microsoft-hosted-azure-devops-agent/ [Accessed: 12th July 2022].