My goal in this blog series is to cover a wide range of topics and issues relating to digital signatures. Let’s get started with a hot question that comes up repeatedly at my talks and webinars, “If an employee leaves our company, and he is removed from the digital signature system, what happens to the documents he signed in the past? Do those signatures remain valid?” Yes, they remain valid.
 And a related question: “Once a document is digitally signed, can the signature be revoked? Suppose the signer is fired, can we revoke some or all of her past signatures?” No.
And a related question: “Once a document is digitally signed, can the signature be revoked? Suppose the signer is fired, can we revoke some or all of her past signatures?” No.
Open standard digital signature technology (we’ll talk more in the future about what that really means) is modeled after traditional pen and ink signature technology, including signature authenticity issues. You may not think of an ink pen as “technology” but it is. Just visit Fahrney’s Pens in DC if you’re not sure! But I digress.
Like a pen and ink signature (a “wet signature”), a digital signature cannot be remotely controlled. If a digital signature is valid at the time the document was signed, then it remains valid forever. Checking the validity can get tricky in various cases, but the signature itself, once valid, stays valid.
If a document has been signed with a wet signature, the document can be “un-signed” by scratching out the signature before the document is distributed. In the same way, a digital signature can be removed from a document before it is distributed. But for both wet and digital signatures, it is difficult or impossible to scratch out/remove your signature from all the copies once the document is distributed.
By design, it is difficult to revoke a signed document. For instance, a contract offer can’t be revoked once it is accepted. Instead, the contract must be cancelled by mutual agreement or via one of the accepted clauses. We say “your signature counts” because it is so hard to revoke your signature. And your signature counts equally for both wet and digital signatures.
What about digital certificate “revocation lists?” Can’t they be used to revoke a signature? Again, no. A revocation list is used by signing software to prevent a revoked certificate from being used to make a new digital signature. It has no effect on documents correctly signed in the past.
Here’s how it works: Each certificate authority, or CA, issues a revocation list. The CA’s revocation list shows the certificates that have been revoked before their expiration time. For example, Joe Employee has a digital certificate issued by his company. He digitally signs a document in June. He leaves the company in July and his certificate is cancelled by adding it to the CA’s revocation list. As a result, he can no longer create valid signatures. But his prior signatures, from before he left, were valid and remain valid.
The recipient of a digitally signed document can verify the document’s signature or signatures. As a part of the process, the recipient’s software checks the CA’s revocation list to ensure that the signer’s certificate was not on the list prior to the time the document was signed.
About the author:

CoSign by ARX
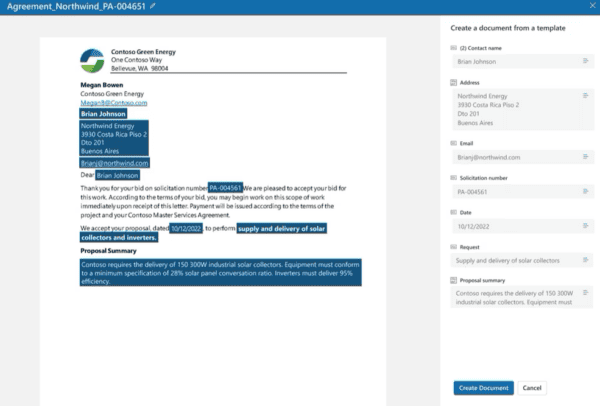
This blog was wrote by Larry Kluger from CoSign by ARX. CoSign by ARX is the strongest and most widely used digital signature solution with millions of users at businesses, governments and cloud services around the world. CoSign is the only digital signature solution that can be seamlessly integrated with SharePoint, SharePoint Online, and related applications such as K2 and Nintex.
By seamlessly integrating digital signatures into existing document-related workflows, applications and services across their organizations, CoSign customers quickly transform slow and expensive signature-dependent processes into quick and efficient paper-free ones. They rapidly reach ROI through significant reductions in process times and paper-related costs, while ensuring trust, integrity and control across their business and IT environments, as well as compliance with the relevant EU legislation and industry-specific regulations.
Check out the 2016 European SharePoint Conference video: