Blog Posts
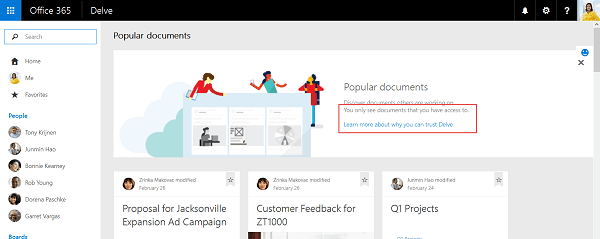
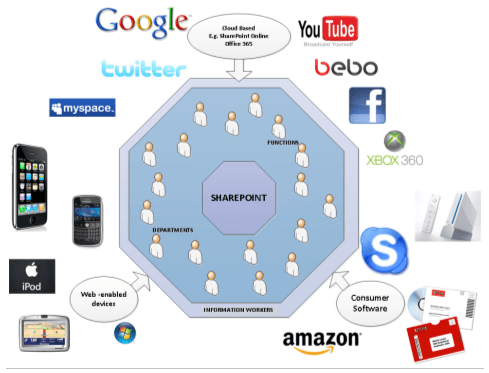
Security is a real issue when we are discussing SharePoint Management. You know that. No wonder one of the most common mistakes enterprises are facing when dealing with SharePoint, is having end users with more access privileges to documents that they should.
It seems a simple problem to solve, but the reality of controlling employee’s access to confidential content, and making sure their access is not too broad, is a challenge for many.
That is why I decided to include, as one of the coverage points of our SharePoint Document Management blog series, some tips about SharePoint permissions, sharing how to give access to resources correctly, how to prevent SharePoint security breaches, and how to plan your permissions without compromising your document management and automation system in SharePoint.