Currently, you can’t create a brand new Watchlist using either of these, you can only update existing Watchlists. The reason is that both of these Logic App Connectors rely on JSON and Watchlists only currently support creation using .csv files. So, for now, both of these currently work in the same fashion and provide the same function, so I would recommend using the Watchlist- Add a new watchlist item, as this one is easier to work with.
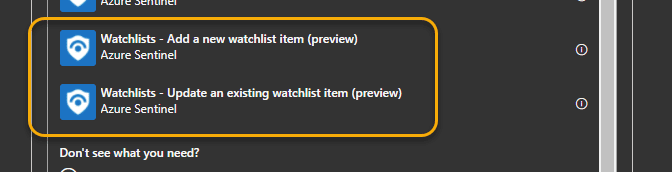
To give you an idea of how this works, here’s an example of something I’ve developed to take an AAD user entity and add it to a list of trusted users.
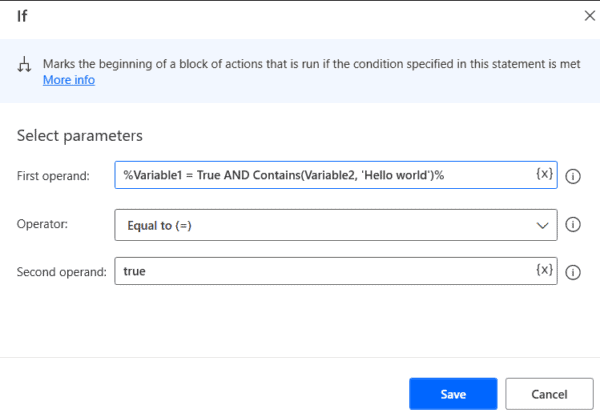
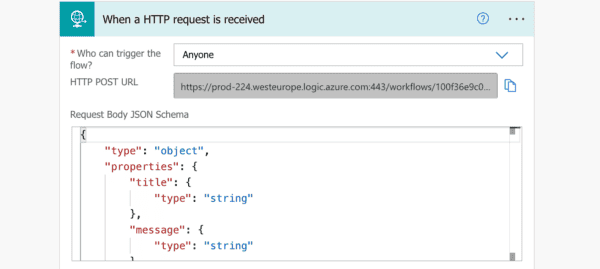
As shown in the image, the lead-up to the Watchlist step is your normal logic flow. Azure Sentinel provides the trigger, then we get the alert and entity information. Then, for every user account captured in the Incident, it will add the AAD name to the Watchlist.
Note the areas I’ve highlighted. The workspace (you need the name, not the ID) isn’t provided in the dynamic list so you have to supply that yourself. The specific watchlist you need to modify, you’ll need to supply that, too. And, finally, you’ll need to use your JSON skills to identify the data column and data value. Fortunately, the data value is available in the dynamic list.
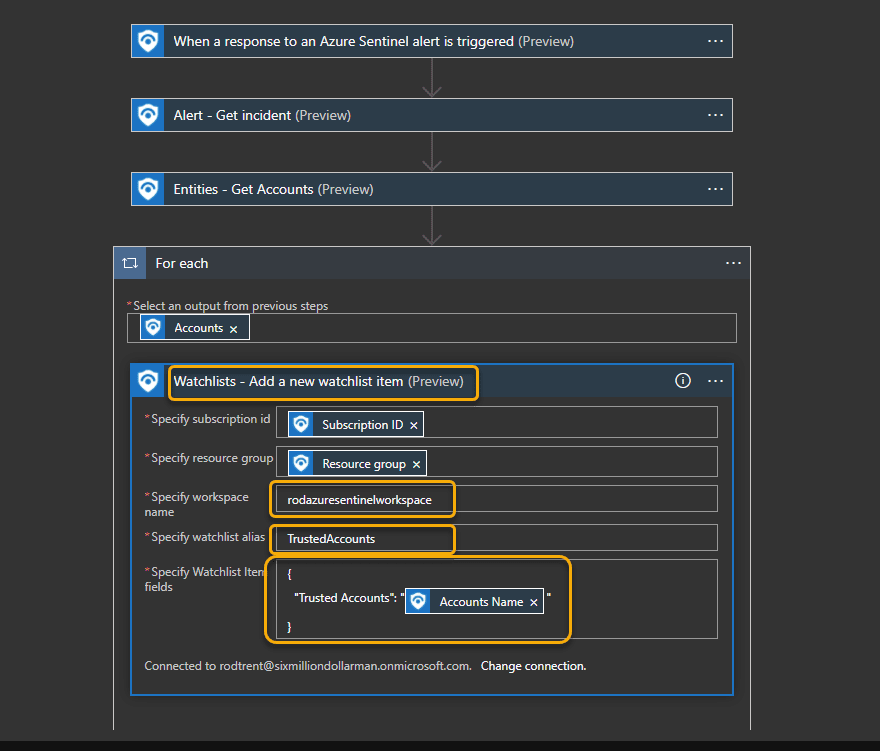
You may want to capture different information to send it to a Watchlist. In my case, I’m capturing the AAD account to use for filtering in my Analytics Rules.
Finally, to use the following to modify your Analytics Rules to take advantage of your work: Use Azure Sentinel watchlists | Microsoft Docs
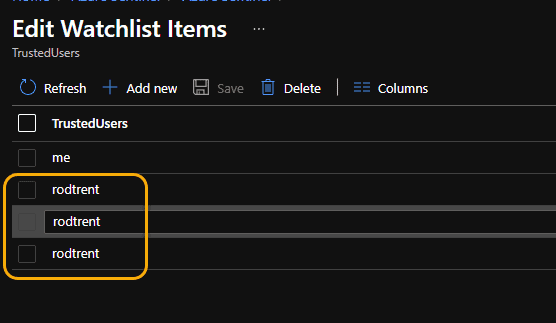
UPDATE: One quick caveat. This goes out to the individual who asked about this – and thanks for doing so because I forgot to cover it earlier. Unfortunately, this will not overwrite existing data. If you run this against a user that already exists in the Watchlist, it will just add a duplicate.
Happy Watchlisting!
This blog is part of Azure Week. Check it out for more great content!
About the Author:
Cybersecurity PFE/Consultant at Microsoft focused on Azure Sentinel, Azure Security Center, and Azure AD.
Reference:
Trent, R. (2021). How to Use the Watchlists Logic App Connector for Azure Sentinel. Available at: https://azurecloudai.blog/2021/06/30/how-to-use-the-watchlists-logic-app-connector-for-azure-sentinel/ [Accessed: 7th July 2021].