How To Simulate Random Errors & Throttling in a Web Application Using Microsoft 365 Developer Proxy
This demo involves the use of the proxy to simulate random errors and throttling in a web application. Garry Trinder (Microsoft) shows how the proxy intercepts requests, injects random errors, and handles throttling scenarios. He explains how to configure the proxy to handle these scenarios, demonstrating how to set failure rates and allowed error codes.
Demo Description:
This demo showcases the utilisation of the Microsoft 365 developer proxy tool for simulating and testing various scenarios, primarily focusing on the injection of random errors and throttling. The presenter begins by demonstrating the invocation of a request to Microsoft Graph via PowerShell, highlighting the proxy’s interception capabilities. The proxy, set as a system-wide intercepting tool, intercepts requests and injects various behaviors into them.
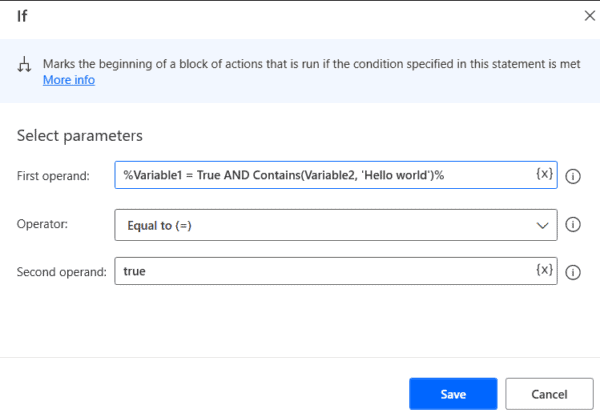
The demo emphasises the process of installing the M365 proxy, which involves the initial setup of a certificate and configuration of default settings stored in the M365 proxy RC JSON file. Garry illustrates how the tool employs plugins to introduce different behaviors and demonstrates the customisation of error injection rates and specific error codes.
The presentation continues with practical examples, where the proxy injects random errors and throttling scenarios into the requests, emphasising the tool’s capacity to modify and test web applications. By using the Graph Explorer as an example, the presenter showcases how the proxy can simulate throttling errors, prompting application developers and testers to ensure their applications effectively handle such scenarios. The versatility of the proxy is highlighted, as it can be easily applied to any web application for testing purposes.
The demo concludes by reiterating the importance of properly stopping the proxy using the “Ctrl+C” command to avoid any lingering registrations causing unexpected behaviors.
Overall, the Demonstration emphasises the M365 developer proxy’s role in efficiently testing and identifying potential application vulnerabilities without requiring extensive knowledge of the application’s code.
STAY UP TO DATE
Continue your learning and register for upcoming webinars here.
Catch up on the latest blogs, eBooks, webinars, and how-to videos.
Not a member? Check out our Learning Hub to unlock all content.
Subscribe to our YouTube channel for the latest community updates.